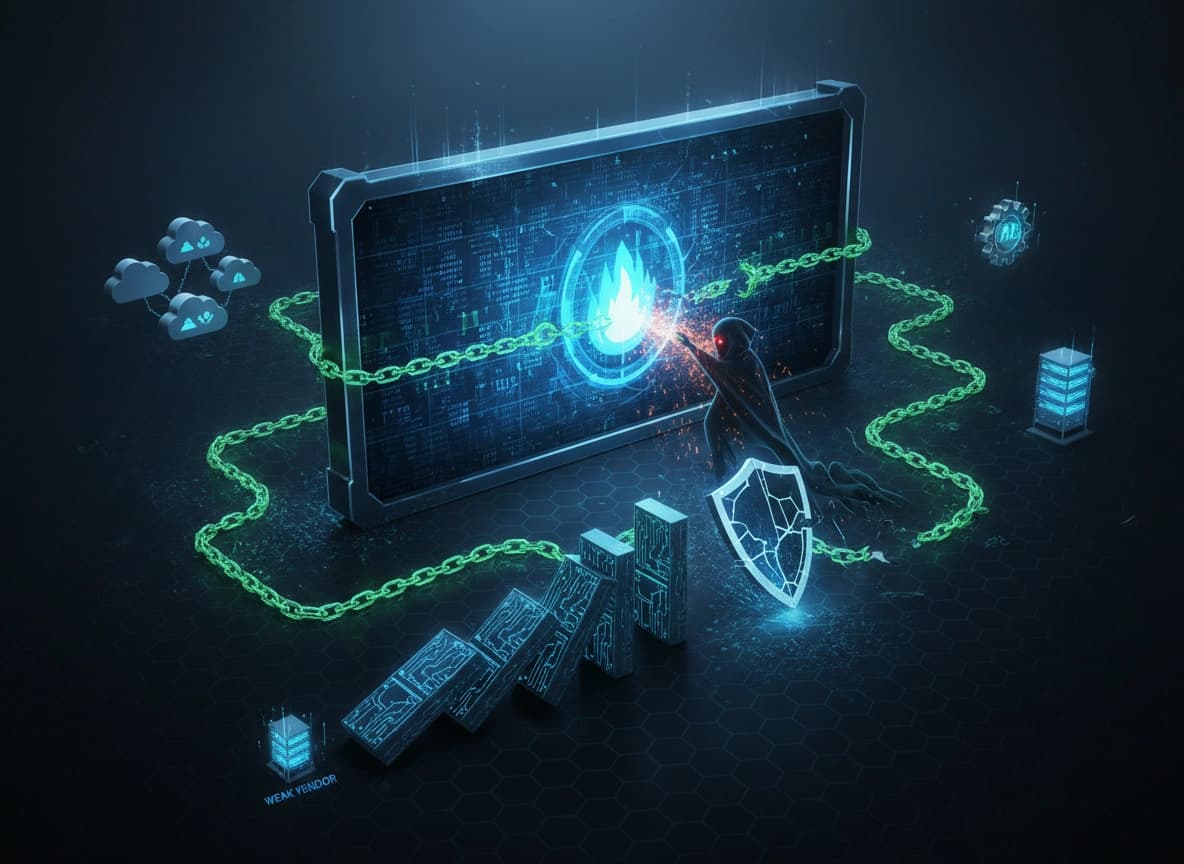
The Supply Chain Domino Effect
Attackers are increasingly bypassing their primary targets by targeting smaller, less secure vendors who have access to the company.Steps of a Supply Chain Attack
-
Identification
An attacker identifies a target, a large financial institution or a government agency. -
Reconnaissance
Instead of attacking the target's security infrastructure (firewalls, EDR, SIEM), the attacker looks for the target's vendors. -
Infiltration
The attacker breaches a small vendor with weak security, such as a software developer with lax password policies or an HVAC contractor with remote access to the target's building systems. -
Pivot
Using the trusted connection belonging to the vendor, the attacker moves laterally into the primary target's environment.