Cyberwarfare has shifted from espionage to a full-scale digital battlefield.

Share this article

Employees are seeking quick and convenient tools to get the job done, whether IT approves them or not. This widespread use of "Shadow IT" is exposing companies to security breaches, data loss, and compliance failures.

As IoT adoption grows, taking security measures is necessary to prevent breaches and protect sensitive data.
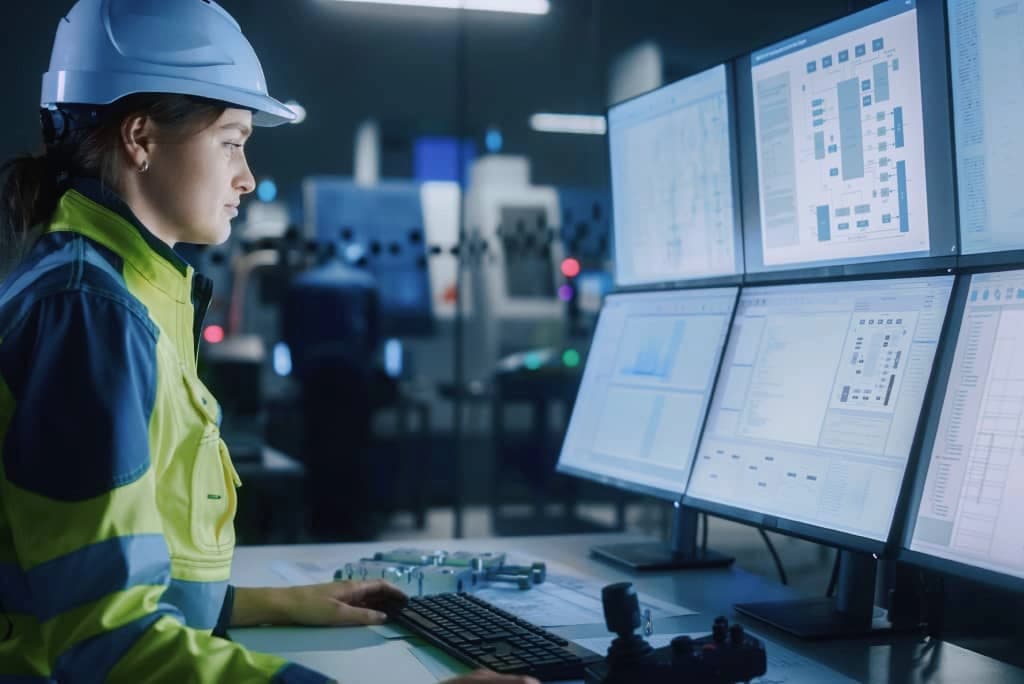
The world’s critical systems, from power grids to water plants, are increasingly under attack. This article explores why nation-state actors are attacking industrial control systems, how they infiltrate them, and what it means for the future of global security.
Subscribe to our newsletter to receive the latest news, updates, and special offers directly in your inbox. Don't miss out!